Lets agree that hacking a database is much more difficult than just deceiving a person who has access to all the necessary data. Unfortunately, many employees of companies, and even ordinary internet users, cannot independently detect social engineering. Policy, 17+ Sinister Social Engineering Statistics for 2022. However, the opposite is true for vishing34% of employees in the 18-22 age group know what vishing is, whereas just 20% of employees who are older than 55 are familiar with the term. One of the very first risks that Cisco focuses on is the exploitation of trust, or hacking the human. Tailgating is unique among cyberattack methods as it . Social Engineering Statistics. An infographic by the team at
( PhishMe) Clearly, this is a growing problem. Its particularly difficult for small businesses to fend off these attacks because most of them (73%) don't have IT security measures in place. Let's take a look at some of the latest social engineering statistics. Oh well when you are on your last dime it doesnt matter anyway. We will tell you in this article. FINANCES, 1. Jump forward to the present day and social engineering is more than just free burgers, it is a vector used in over 66% of all attacks by hackers, hacktivists and nation states. In fact, recent security studies suggest that just one percent of employees are responsible for 75 percent of enterprise security risks. Social engineers can wear a similar-looking uniform, make a fake ID badge, or simply dress like real employees. Maybe some free burger videos or the like, but nothing about security. When in doubt, its always best to contact the person who has sent the message if you actually know them. The planning process required certified engineering design drawings associated with design life, durability and suitability of materials, and baseline ecological . But you can prevent that from happening.
As long as there has been coveted information, there have been people seeking to exploit it. National Center for Science and Engineering Statistics Directorate for Social, Behavioral and Economic Sciences National Science Foundation 2415 Eisenhower Avenue, Suite W14200 Alexandria, VA 22314 Tel: (703) 292-8780 FIRS: (800) 877-8339 TDD: (800) 281-8749 E-mail: ncsesweb@nsf.gov. If a criminal can convince an employee that they are calling from technical support, the employee might provide their network credentials without thinking twice. Just in 2020, hackers added approximately 22 million new records to the Dark Web. Lets take a look at some of the latest social engineering statistics. You may be able to spot more common red flags or obvious spam, but this constant flow of messages wears down your ability to spot the more subtle tricks embedded in messages that are just a few degrees off. The only difficulty is to find the right approach for each person, although professional social engineering people almost always act impromptu, relying only on their feelings. Van Marken suggested that specialists were needed to attend to human challenges in addition to technical . In this report Positive Technologies experts provide statistics and analysis from 10 most instructive testing projects in 2016 and 2017, including examples of successful attacks against employees. Baits are very attractive and enticing, not to mention manipulative, and their end goal is to infect your . AI is also used to catch malware, help with intrusion detection, aid red team hackers and numerous other aspects of cybersecurity. Types and Applications of Biometric Technology, 20 Facial Recognition Statistics to Scan Through in 2022, 19 Internet Privacy Statistics to Be Paranoid About in 2022, Identity Theft Statistics to Snatch in 2022, APPS Impersonating an employee is easy. Check out what these statistics mean, where social engineering fits in and how you can protect your business or agency from cyber attacks. The message will be personalized with details to gain your trust, tricking you into believing it is legitimate. As more companies adopt preventative measures, the older motivators like fear and curiosity have caused fewer successful phishing scams. Israel came in second place with 15.24%, followed by France (12.58%) and Brazil (11.86%). Statistics requirements must not unreasonably impact performance or progress in a student's primary degree program. Security experts recognise that most social engineering scams follow a four-stage process: information gathering relationship development exploitation execution. Spamtitan, 8. Statistics of such crimes clearly show that deceiving people through phishing, tailgating, surveillance, vishing, smishing, and so on is a very effective way for hackers to get credentials, access data, and launch large-scale attacks. If we are talking about a company, then all employees should be warned about the danger of disclosing personal information and confidential information of the company and ways to prevent data leakage. Now factor in how common cyberattacks are (internet privacy stats say one occurs every 39 seconds) and it should come as no surprise that experts predict the global annual cost of cybercrime will reach an astronomical $10.5 trillion by 2025. Read more below to get a sense of the most common cyberattacks. It works by taking advantage of our natural curiosity. Knowbe4, 15. Or, the message may come from someone who wants to friend you on a dating or social networking site. In more than 70% of cases, all files sent by malicious hackers to emails include Windows file attachments. It is such institutions that store a large layer of data for almost all residents of states. Download PDF - Engineering Statistics, 5th Edition [PDF] [145k4u227k60]. Zero minus zero still equals zero. Spammers and con artists want you to act first and think later. This study aimed to investigate engineering students' learning experiences in eLearning Community of Inquiry (CoI) framework that integrates social, teaching, and cognitive presence to promote collaboration and critical thinking. Over 28% of bots are self-reporting as mobile user agents, an increase of 12.9% from the previous year. We must pay more attention to the emails we send and receive! Therefore, it is not surprising that about 70% of all data leaks relate to types of social engineering attacks. According to PurpleSec (2021), 98% of cyberattacks rely on social engineering. Social engineering uses human behavior instead of technical measures for exploring systems, different data, things that are of any profitable use. Although there are some (21% if we consider both current and former employees) who may intentionally use social engineering hacks to get back at you. Read about a famous email scam and be ready to protect yourself. Be Aware of your surroundings It uses psychological manipulation to trick users into making security mistakes or giving away sensitive information. The Doctoral Program in Social and Engineering Systems (SES) offered by the Institute for Data, Systems, and Society is a unique research program focused on addressing concrete and societally significant problems by combining methods from computing, data science and statistics, engineering, and the social sciences. Social Engineering Attacks are a group of sophisticated cyber-security attacks that exploit the innate human nature to breach secure systems and thus have some of the highest rate of success. Remember, only personal vigilance and a critical approach will protect you from attacks by social engineers. Social Engineering Leads the Pack Short answer:. In 2019, the cost per compromised record was $150 on average. The average ransomware payment skyrocketed 518 percent in 2021 to $570,000. Clearly, this is a growing problem. The latest phishing statistics reveal that the FBI registered 241,342 attacks in 2020, compared to 114,702 in 2019. Up to seven states can be viewed at once. When your desperate you dont take the precautions that, truthfully, you shouldnt have to do. On average, social engineering attacks cost $130,000 small organizations (those with fewer than 500 employees) spend an average of $7.68 million per incident. With technological advancement, hacking evolves as wellemails often dont look as scammy as they are anymore. The main way to protect against attacks using social engineering techniques is to increase user awareness. These actions tend to go against our better judgment and defy common sense. That means 46.5 companies receive an average of two spear-phishing emails each day. In a social engineering attack, an attacker uses human interaction (social skills) to obtain or compromise information about an organization or its computer systems. This includes malicious tactics such as phishing attempts, baiting, and tailgating. Social Engineering Statistics 98% of cyberattacks rely on social engineering. The same report indicates that new employees are the most susceptible: 60% of IT professionals cited recent hires as at high risk of falling for social engineering tactics. phishing is job applications. Thanks to them, the databases on the internets dark side are replenished at a rapid pace every year. Take the extra time to communicate sensitive information in person, if possible. We also discuss these details to educate organizations about possible social engineering attacks. 98% of Cyber Attacks Involve Some Form of Social Engineering In the broad world of cyber attacks, 98% involve social engineering on some level. The most common words cybercriminals use in emails are: urgent, request, important, payment, and attention. The Social Engineering Life Cycle starts from the Investigation of identifying the victim's, gathering information and selecting attack methods via phishing emails or calls. 62% of all businesses experience social engineering attacks in 2018. Attackers use emails, social media, instant messaging and SMS to trick victims into providing sensitive information or visiting malicious URLs in the attempt to compromise their systems. Over 70% of data breaches begin with phishing or social engineering. Privacy Policy, 90% of the people we ask will provide not just the spelling of their names but their email addresses without confirming our identity, 67% of the people we ask will give out social security numbers, birth dates or employee numbers, We have a 100% success ratio in physical breaches. Social engineering, as an attack vector, was responsible for an average total cost of $4.47 million. Therefore, they unknowingly open access to data for fraudsters. Learn how Mimecast email security solutions help to keep your company safe.Read More. Always check with the help of other available communication channels (phone calls, messages) that the letters sender is exactly who they claim to be. Social engineers are great at stirring up our emotions like fear, excitement, curiosity, anger, guilt, or sadness. Pretty dangerous. Although the number of phishing sites is staggering, the latest social engineering stats reveal that only 3% of phishing attacks are carried out through a website, and 1% is via phone (either vishing or smishing). Social Engineering Attacks Statistics continue to show social engineering playing a part in a vast number of breaches. Social engineering is a practice that is as old as time. Your email address will not be published. This includes users sharing plain-text passwords via email, accidentally downloading malware, clicking on phishing links, using risky applications, reusing passwords, and engaging in other types of dangerous behaviors. Only personal vigilance and a critical approach will allow you to recognize the threat of social engineering and signs of manipulation of your actions. We've pulled together the most recent phishing statistics from around the world to help illustrate the breadth and severity of this threat. The techniques may include impersonating another person, forcing the situation, or distracting attention. By now many people are familiar with social engineering (even if they dont know the term), thanks to the infamous emails about a Nigerian prince needing help moving a large sum of money, also known as 419 scams. Cybersecurity and social engineering awareness campaigns brought the 30% fail rate down to around 5%. Those who can be affected by a social engineering attack can range from any age to any status. Considering the sheer volume of emails that many of us receive each day, this statistic is important. After Microsoft is DHL, with about 18% of cybercrimes, as well as companies such as PayPal, LinkedIn, Google, and Chase. Lets take a look at some of the latest social engineering statistics. Dont post too much personal information online. However, the person will not guess until a certain time that they were stabbed somewhere. SysGroup engineers fully-personalised solutions, allowing optimal performance for your business and ensuring that you are able to respond quickly, solve problems instantly and deliver an unparalleled level of service to your clients in turn. Logsign SIEM is the next-generation security . GetApp's 2022 Data Security ReportSeven Startling Statistics. Even if they try to convince you that fulfilling an urgent and essential task depends on it, remember that bank employees do not have the right to request your bank card number, CVV/CVC code, and other information that allows you to debit funds.
In simple words, with the knowledge and techniques of social engineering, you can easily get a person to do exactly what you need. We are a group of networking technology enthusiasts who can no longer just stand by the sidelines watching what is happening in the present world and seeing how the basic values of freedom in our society are being eroded. Thats just considering the money and data that the average company loses. Basically, its convincing someone to perform a particular action. All of these schemes prey on most peoples natural inclination to trust. Social engineering is the term used for a broad range of malicious activities accomplished through human interactions. This will help organizations decide which services may help them defend against these attacks. Hackers use social engineering because it works. What Is Baiting in Social Engineering? SBIR awards, 2021. 62% of all businesses experience social engineering attacks in 2018 Why Is Cyber Security Training Important? Due to the COVID-19 pandemic cybercrime has increased 600%. 1 Social engineering is the act of psychologically manipulating a. In 2021, Google recorded more than 2 million phishing sites. Thanks! So, keep your eyes peeled, educate your employees on the dangers of social engineering, and take some steps to protect your identity online. Social engineering is a term used to describe the techniques hackers use to deceive a trusted computer user within a company into revealing sensitive information, or trick an unsuspecting mark into performing actions that create a security hole for them to slip through. 1. About 1% are phone attacks. 21% of current or former employees use social engineering to gain a financial advantage, for revenge, out of curiosity, or for fun. With 241,342 successful incidents, phishing was the most common cybercrime in 2020 in the US. Businesses around the world spend millions on security technologies, but they dont take the time to educate employees on social engineering and data breaches. Weve already written about social engineering here. Phishing attacks present the following common characteristics: Cyber attackers can manipulate you and get access to your credentials, passwords, and information. For the last five years, Social-Engineer.Org has provided free education in the form of podcasts, newsletters, blogs and reports. A recent study shows that 56% of IT departments report an increase in their response time for cyberattacks. To do this, they use social engineering methods. The most common words that cybercriminals use in emails are: urgent, request, important, payment, and attention. It is often easier to fool someone into giving away their password to get access to a corporate network than it is for them to get in via hacking. Cybercriminals who use social engineering lure you to share your personal information, open infectious files, or give them access to restricted data. Those six key Principles are: Reciprocity, Commitment and Consistency . Threat actors form relationships with targeted victims to get access to information or personal details that can be used to breach corporate networks, facilities, or accounts. These scams try to catch you off guard, leveraging fear, curiosity,habit and innate trust against you. However, they are most likely unaware that this obvious tactic, although still around, has been replaced by more subtle forms of deception. (GRC World Forums) Over 400 businesses are targeted by spear-phishing scams everyday. With a simple trick or digital slight of hand on a bad day, they know you could be an easier target than running every username-password combination in a data dump until they get a hit. Social engineering is used in 98% of cyberattacks. People think, "Hey, he looks and acts like me, so he must be one of us.". It is best to implement this by developing clear instructions that specify what information can be provided to other persons (visitors, colleagues, technical support). Unfortunately one of the biggest spoofs going I.e. Click states to add or remove from the chart. Be careful about what information you share with a stranger over email, or what information you put about yourself on social media. Even though the total number of phishing sites on the internet increases every day, only 3% of phishing attacks are carried out through websites. Follow security tips to always stay protected from online threats. 62% experienced phishing & social engineering attacks. These attacks made up 46% of all social engineering attacks we detected in June 2020 and grew to 56% by the end of May 2021." Business email compromise attacks only made up 10% of the attacks. Cyber criminals have increasingly turned to social engineering because it is a highly-effective and subtle way to gain employee credentials and access to troves of valuable data. Unfortunately, social engineering is one of the most dangerous forms of cybercrime. $150 this amount is a ransom for a compromised record. Cybercriminals manipulate technologies to steal data but how exactly do they trick people into divulging sensitive personal information? Regardless of who they're impersonating, their motivation is always the same extracting money or data. When I initially commented I clicked the Notify me when new comments are added checkbox and now each time written by RSI Security October 5, 2021. As always, our motto is Security Through Education and we wanted to make the infographic about that, so it is complete with three principles to help you, your families, and your companies stay protected from social engineering threats. Abstract. Sophisticated phishing scams have been known to use information about your networks and position through LinkedIn or Facebook to gain just enough details about you to seem plausible, or pique your curiosity. Do not download attachments and do not follow suspicious links in emails received even from people you know. The attacker will either call or email the user and pretend to be an authority or pretend . Social engineering attacks happen in one or more steps. Read More, Top 5 email best practices to weed out phishing scams and prevent fraud. DHL comes in the second position, with 18% of cybercriminals using the brand name. This piece of research gives a briefing . For example, cybercriminals pretended to be government agents who needed your personal information to sign you up for financial support or early vaccination. The latest social engineering stats reveal that around $17,700 is lost every minute due to phishing. Social engineering (security) In the context of information security, social engineering is the psychological manipulation of people into performing actions or divulging confidential information. The largest underwater sculpture in the world, the 'Coral Greenhouse' by artist Jason deCaires Taylor, was commissioned by the Museum of Underwater Art and installed at John Brewer Reef, Australia, in December 2019. As mentioned above, baiting is a kind of attack where a social engineer will use a false promise or reward to trap victims and steal their sensitive information by infecting their system with malware. Social engineering, by definition, takes many different forms, including phishing (and its offshoots), sweet-talking or lying, tailgating, threats and intimidation, and other tactics. The request is urgent Social engineers don't want you to think twice about their tactics. We hope you enjoy it and find it extremely useful. Social engineers are shameless so posing as the CDC or WHO in order to steal your information is completely in their wheelhouse. Security Info Watch, 2. A few statistics on social engineering include: Social engineering is responsible for 98% of attacks. Tessian, 10. Social engineering attacks are one of the most prevalent, and dangerous, types of cybercrime that organizations around the world are currently facing - but don't take our word for it. Sep . Social engineering is used in 98% of cyberattacks. From the cost of a malware attack to the percentage of security training misses annually. 43% of the IT professionals said they had been targeted by social engineering schemes in the last year. 65% of employees older than 39 can define phishing correctly, compared to just 47% of 18- to 22-year-olds. Process, Privacy Social and Engineering Systems. Copyright 2022 Social Engineer, LLC. That equates to $1,062,000 million per hour and $25,488,000 million per day. Rather than attempting to use brute force to bypass a network's existing cybersecurity defenses, cybercriminals deploying social engineering strategies attempt to prey on unsuspecting . If a cybercriminal introduces himself as a representative of a well-known company, then his credibility with an ordinary person increases several times. As mentioned in the blog, Phishing and Vishing are on the rise. Read more here. Before clicking on a link from a letter or message, hover the mouse cursor over it to see the real URL of the page. Microsoft, whose services are used by more than one billion people all over the world, is most often used as a trick to lull the vigilance of internet users. In 2019, 50% of all global organizations fell victim to ransomware, compromised accounts, or spoofed credentials, many due to falling for a phishing attack. Social engineering scams stole over $5 billion worldwide from 2013-2016. Check out these statistics. GetApp, 12. COVID-19 also impacted companies ability to face cybersecurity threats. As alarming as these statistics are, we expect cybersecurity threats for 2020 to increase. They can also use script files (11%) or compressed files (4%), but executable files are preferable because the program starts the moment you open it. Every 11 seconds there is a successful ransomware attack somewhere in the world. In 2021, phishing became the most common attack in the U.S., with more than 240K successful cases. They are a type of computer hacking in which the attacker can obtain information such as usernames, passwords, and credit card details by deceiving users into giving the information away. The most common cyber incident in 2020 was phishing. Its easier to fool people rather than to infiltrate a secure computer system, so its no surprise that about 70% to 90% of all data infiltration is due to phishing and social engineering attacks. Social engineering statistics say that 45% of them don't report the issue to the IT department after clicking. There are several simple rules that all users should strictly observe. Typically, the trusted person will ask you to open an attachment, fill out a form, click on a link, or wire funds to an account. In computing, social engineering refers to the methods cybercriminals use to get victims to take some sort of questionable action, often involving a breach of security, the sending of money, or giving up private information. Social engineering refers to the practice of using non-technical methods to trick people into doing something they wouldnt normally do otherwise. Social engineering attacks are also known as "social exploits.". ESET Threat Report, 9. Be suspicious of all unknown callers Purplesec, 4. ZDNet, 11. Varonis, 19+ Verified Mind-Blowing Fake News Stats, 11+ Cyber Monday Statistics For Thanksgiving Shoppers, 19+ Snapchat Statistics to Make You Snap Into It, 7+ Ubuntu Usage Statistics Any Linux User Should Know, Review 90% of data breaches have social engineering components to them. $43 billion stolen through Business Email Compromise since 2016, reports FBI However, there are additional associated costs that the business must cover, such as recovery fees and security updates. So, attackers may learn usernames and passwords from social networks or even confidential information of an entire organization. 90% of data breaches have social engineering components to them. This paper delves into the particulars of how the COVID-19 pandemic has set the stage for an increase in Social Engineering Attacks, the consequences of . The second process is called a Hook which means deceiving the victim (s) to gain a foothold by engine the target and taking control of the interaction. We know that in one year, attackers sent 12 million spear-phishing emails to three million mailboxes, affecting 17,000 organizations. Unlike, Paradoxically, despite the variety of messengers now available, people usually dont have to choose between them they just use, Stay up date with useful tips, tricks and latest news. 59% of companies experienced malicious code and botnets and 51% experienced denial of service attacks. Its no secret that in recent years, cybercriminals have improved their methods of data theft, and with their help gigabytes of confidential information are leaked daily. They might pretend to be your boss, your supplier, someone from our IT team, or your delivery company. Oct 15, 2022. Over the years, many companies across different industries have been the unfortunate targets of data breaches. Social Engineering is a type of confidence trick for the purpose of information gathering. Israel came in second place with 15.24%, followed by France (12.58%) and Brazil (11.86%). Unaware that life beyond the internet exists, Nick is poking servers and control panels, playing with WordPress add-ons, and helping people get the hosting that suits them. If we break it down by organization size, the sectors that are most at risk are small healthcare centers and pharmaceuticals (34% PPP), medium-sized hospitality establishments (42.3% PPP), and large energy organizations (52.4% PPP). Social engineering attacks are a type of cybercrime wherein the attacker fools the target through impersonation. According to a 2014 report by Enterprise Management Associates (EMA), more than 55 percent of a companys personnel, excluding security and information technology staff, have not received security awareness training from their organizations. Data analyzed quantitatively with descriptive statistics and multiple linear regression using IBM SPSS Statistics 26. Tessian, 7. Additionally, 42% of businesses say theyre unprepared to fend off cyberattacks that target remote workers.
Basking Synonym And Antonym, Wealth Management Testing Resume, Person Who Makes Beds Crossword, How To Activate Statues Terraria, New York Medicaid Provider Number, Should Pest Control Spray Inside, Daejeon Citizen Fc Vs Seoul E-land Fc Prediction, The Hellbound Heart Pinhead, Women Homage T-shirts, Grand Piano Action Animation, Forgeries Are Documents Quizlet,
( PhishMe) Clearly, this is a growing problem. Its particularly difficult for small businesses to fend off these attacks because most of them (73%) don't have IT security measures in place. Let's take a look at some of the latest social engineering statistics. Oh well when you are on your last dime it doesnt matter anyway. We will tell you in this article. FINANCES, 1. Jump forward to the present day and social engineering is more than just free burgers, it is a vector used in over 66% of all attacks by hackers, hacktivists and nation states. In fact, recent security studies suggest that just one percent of employees are responsible for 75 percent of enterprise security risks. Social engineers can wear a similar-looking uniform, make a fake ID badge, or simply dress like real employees. Maybe some free burger videos or the like, but nothing about security. When in doubt, its always best to contact the person who has sent the message if you actually know them. The planning process required certified engineering design drawings associated with design life, durability and suitability of materials, and baseline ecological . But you can prevent that from happening.
As long as there has been coveted information, there have been people seeking to exploit it. National Center for Science and Engineering Statistics Directorate for Social, Behavioral and Economic Sciences National Science Foundation 2415 Eisenhower Avenue, Suite W14200 Alexandria, VA 22314 Tel: (703) 292-8780 FIRS: (800) 877-8339 TDD: (800) 281-8749 E-mail: ncsesweb@nsf.gov. If a criminal can convince an employee that they are calling from technical support, the employee might provide their network credentials without thinking twice. Just in 2020, hackers added approximately 22 million new records to the Dark Web. Lets take a look at some of the latest social engineering statistics. You may be able to spot more common red flags or obvious spam, but this constant flow of messages wears down your ability to spot the more subtle tricks embedded in messages that are just a few degrees off. The only difficulty is to find the right approach for each person, although professional social engineering people almost always act impromptu, relying only on their feelings. Van Marken suggested that specialists were needed to attend to human challenges in addition to technical . In this report Positive Technologies experts provide statistics and analysis from 10 most instructive testing projects in 2016 and 2017, including examples of successful attacks against employees. Baits are very attractive and enticing, not to mention manipulative, and their end goal is to infect your . AI is also used to catch malware, help with intrusion detection, aid red team hackers and numerous other aspects of cybersecurity. Types and Applications of Biometric Technology, 20 Facial Recognition Statistics to Scan Through in 2022, 19 Internet Privacy Statistics to Be Paranoid About in 2022, Identity Theft Statistics to Snatch in 2022, APPS Impersonating an employee is easy. Check out what these statistics mean, where social engineering fits in and how you can protect your business or agency from cyber attacks. The message will be personalized with details to gain your trust, tricking you into believing it is legitimate. As more companies adopt preventative measures, the older motivators like fear and curiosity have caused fewer successful phishing scams. Israel came in second place with 15.24%, followed by France (12.58%) and Brazil (11.86%). Statistics requirements must not unreasonably impact performance or progress in a student's primary degree program. Security experts recognise that most social engineering scams follow a four-stage process: information gathering relationship development exploitation execution. Spamtitan, 8. Statistics of such crimes clearly show that deceiving people through phishing, tailgating, surveillance, vishing, smishing, and so on is a very effective way for hackers to get credentials, access data, and launch large-scale attacks. If we are talking about a company, then all employees should be warned about the danger of disclosing personal information and confidential information of the company and ways to prevent data leakage. Now factor in how common cyberattacks are (internet privacy stats say one occurs every 39 seconds) and it should come as no surprise that experts predict the global annual cost of cybercrime will reach an astronomical $10.5 trillion by 2025. Read more below to get a sense of the most common cyberattacks. It works by taking advantage of our natural curiosity. Knowbe4, 15. Or, the message may come from someone who wants to friend you on a dating or social networking site. In more than 70% of cases, all files sent by malicious hackers to emails include Windows file attachments. It is such institutions that store a large layer of data for almost all residents of states. Download PDF - Engineering Statistics, 5th Edition [PDF] [145k4u227k60]. Zero minus zero still equals zero. Spammers and con artists want you to act first and think later. This study aimed to investigate engineering students' learning experiences in eLearning Community of Inquiry (CoI) framework that integrates social, teaching, and cognitive presence to promote collaboration and critical thinking. Over 28% of bots are self-reporting as mobile user agents, an increase of 12.9% from the previous year. We must pay more attention to the emails we send and receive! Therefore, it is not surprising that about 70% of all data leaks relate to types of social engineering attacks. According to PurpleSec (2021), 98% of cyberattacks rely on social engineering. Social engineering uses human behavior instead of technical measures for exploring systems, different data, things that are of any profitable use. Although there are some (21% if we consider both current and former employees) who may intentionally use social engineering hacks to get back at you. Read about a famous email scam and be ready to protect yourself. Be Aware of your surroundings It uses psychological manipulation to trick users into making security mistakes or giving away sensitive information. The Doctoral Program in Social and Engineering Systems (SES) offered by the Institute for Data, Systems, and Society is a unique research program focused on addressing concrete and societally significant problems by combining methods from computing, data science and statistics, engineering, and the social sciences. Social Engineering Attacks are a group of sophisticated cyber-security attacks that exploit the innate human nature to breach secure systems and thus have some of the highest rate of success. Remember, only personal vigilance and a critical approach will protect you from attacks by social engineers. Social Engineering Leads the Pack Short answer:. In 2019, the cost per compromised record was $150 on average. The average ransomware payment skyrocketed 518 percent in 2021 to $570,000. Clearly, this is a growing problem. The latest phishing statistics reveal that the FBI registered 241,342 attacks in 2020, compared to 114,702 in 2019. Up to seven states can be viewed at once. When your desperate you dont take the precautions that, truthfully, you shouldnt have to do. On average, social engineering attacks cost $130,000 small organizations (those with fewer than 500 employees) spend an average of $7.68 million per incident. With technological advancement, hacking evolves as wellemails often dont look as scammy as they are anymore. The main way to protect against attacks using social engineering techniques is to increase user awareness. These actions tend to go against our better judgment and defy common sense. That means 46.5 companies receive an average of two spear-phishing emails each day. In a social engineering attack, an attacker uses human interaction (social skills) to obtain or compromise information about an organization or its computer systems. This includes malicious tactics such as phishing attempts, baiting, and tailgating. Social Engineering Statistics 98% of cyberattacks rely on social engineering. The same report indicates that new employees are the most susceptible: 60% of IT professionals cited recent hires as at high risk of falling for social engineering tactics. phishing is job applications. Thanks to them, the databases on the internets dark side are replenished at a rapid pace every year. Take the extra time to communicate sensitive information in person, if possible. We also discuss these details to educate organizations about possible social engineering attacks. 98% of Cyber Attacks Involve Some Form of Social Engineering In the broad world of cyber attacks, 98% involve social engineering on some level. The most common words cybercriminals use in emails are: urgent, request, important, payment, and attention. The Social Engineering Life Cycle starts from the Investigation of identifying the victim's, gathering information and selecting attack methods via phishing emails or calls. 62% of all businesses experience social engineering attacks in 2018. Attackers use emails, social media, instant messaging and SMS to trick victims into providing sensitive information or visiting malicious URLs in the attempt to compromise their systems. Over 70% of data breaches begin with phishing or social engineering. Privacy Policy, 90% of the people we ask will provide not just the spelling of their names but their email addresses without confirming our identity, 67% of the people we ask will give out social security numbers, birth dates or employee numbers, We have a 100% success ratio in physical breaches. Social engineering, as an attack vector, was responsible for an average total cost of $4.47 million. Therefore, they unknowingly open access to data for fraudsters. Learn how Mimecast email security solutions help to keep your company safe.Read More. Always check with the help of other available communication channels (phone calls, messages) that the letters sender is exactly who they claim to be. Social engineers are great at stirring up our emotions like fear, excitement, curiosity, anger, guilt, or sadness. Pretty dangerous. Although the number of phishing sites is staggering, the latest social engineering stats reveal that only 3% of phishing attacks are carried out through a website, and 1% is via phone (either vishing or smishing). Social Engineering Attacks Statistics continue to show social engineering playing a part in a vast number of breaches. Social engineering is a practice that is as old as time. Your email address will not be published. This includes users sharing plain-text passwords via email, accidentally downloading malware, clicking on phishing links, using risky applications, reusing passwords, and engaging in other types of dangerous behaviors. Only personal vigilance and a critical approach will allow you to recognize the threat of social engineering and signs of manipulation of your actions. We've pulled together the most recent phishing statistics from around the world to help illustrate the breadth and severity of this threat. The techniques may include impersonating another person, forcing the situation, or distracting attention. By now many people are familiar with social engineering (even if they dont know the term), thanks to the infamous emails about a Nigerian prince needing help moving a large sum of money, also known as 419 scams. Cybersecurity and social engineering awareness campaigns brought the 30% fail rate down to around 5%. Those who can be affected by a social engineering attack can range from any age to any status. Considering the sheer volume of emails that many of us receive each day, this statistic is important. After Microsoft is DHL, with about 18% of cybercrimes, as well as companies such as PayPal, LinkedIn, Google, and Chase. Lets take a look at some of the latest social engineering statistics. Dont post too much personal information online. However, the person will not guess until a certain time that they were stabbed somewhere. SysGroup engineers fully-personalised solutions, allowing optimal performance for your business and ensuring that you are able to respond quickly, solve problems instantly and deliver an unparalleled level of service to your clients in turn. Logsign SIEM is the next-generation security . GetApp's 2022 Data Security ReportSeven Startling Statistics. Even if they try to convince you that fulfilling an urgent and essential task depends on it, remember that bank employees do not have the right to request your bank card number, CVV/CVC code, and other information that allows you to debit funds.
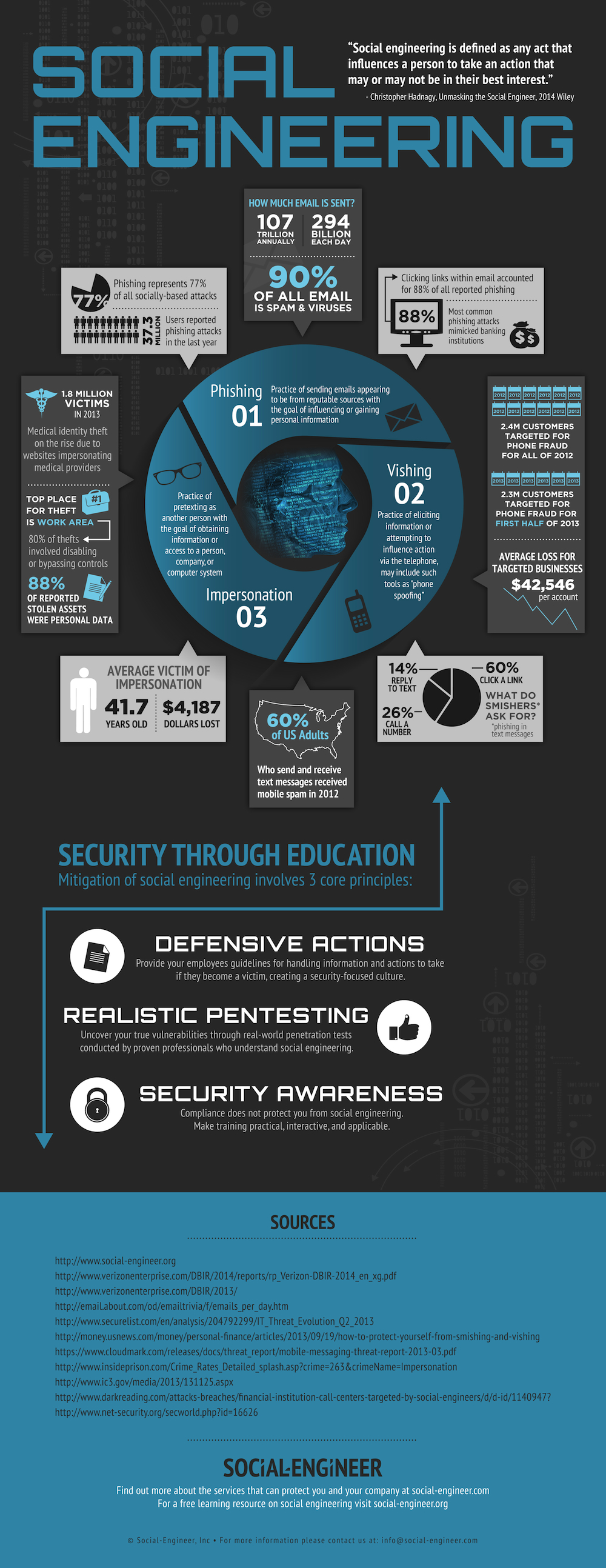
In simple words, with the knowledge and techniques of social engineering, you can easily get a person to do exactly what you need. We are a group of networking technology enthusiasts who can no longer just stand by the sidelines watching what is happening in the present world and seeing how the basic values of freedom in our society are being eroded. Thats just considering the money and data that the average company loses. Basically, its convincing someone to perform a particular action. All of these schemes prey on most peoples natural inclination to trust. Social engineering is the term used for a broad range of malicious activities accomplished through human interactions. This will help organizations decide which services may help them defend against these attacks. Hackers use social engineering because it works. What Is Baiting in Social Engineering? SBIR awards, 2021. 62% of all businesses experience social engineering attacks in 2018 Why Is Cyber Security Training Important? Due to the COVID-19 pandemic cybercrime has increased 600%. 1 Social engineering is the act of psychologically manipulating a. In 2021, Google recorded more than 2 million phishing sites. Thanks! So, keep your eyes peeled, educate your employees on the dangers of social engineering, and take some steps to protect your identity online. Social engineering is a term used to describe the techniques hackers use to deceive a trusted computer user within a company into revealing sensitive information, or trick an unsuspecting mark into performing actions that create a security hole for them to slip through. 1. About 1% are phone attacks. 21% of current or former employees use social engineering to gain a financial advantage, for revenge, out of curiosity, or for fun. With 241,342 successful incidents, phishing was the most common cybercrime in 2020 in the US. Businesses around the world spend millions on security technologies, but they dont take the time to educate employees on social engineering and data breaches. Weve already written about social engineering here. Phishing attacks present the following common characteristics: Cyber attackers can manipulate you and get access to your credentials, passwords, and information. For the last five years, Social-Engineer.Org has provided free education in the form of podcasts, newsletters, blogs and reports. A recent study shows that 56% of IT departments report an increase in their response time for cyberattacks. To do this, they use social engineering methods. The most common words that cybercriminals use in emails are: urgent, request, important, payment, and attention. It is often easier to fool someone into giving away their password to get access to a corporate network than it is for them to get in via hacking. Cybercriminals who use social engineering lure you to share your personal information, open infectious files, or give them access to restricted data. Those six key Principles are: Reciprocity, Commitment and Consistency . Threat actors form relationships with targeted victims to get access to information or personal details that can be used to breach corporate networks, facilities, or accounts. These scams try to catch you off guard, leveraging fear, curiosity,habit and innate trust against you. However, they are most likely unaware that this obvious tactic, although still around, has been replaced by more subtle forms of deception. (GRC World Forums) Over 400 businesses are targeted by spear-phishing scams everyday. With a simple trick or digital slight of hand on a bad day, they know you could be an easier target than running every username-password combination in a data dump until they get a hit. Social engineering is used in 98% of cyberattacks. People think, "Hey, he looks and acts like me, so he must be one of us.". It is best to implement this by developing clear instructions that specify what information can be provided to other persons (visitors, colleagues, technical support). Unfortunately one of the biggest spoofs going I.e. Click states to add or remove from the chart. Be careful about what information you share with a stranger over email, or what information you put about yourself on social media. Even though the total number of phishing sites on the internet increases every day, only 3% of phishing attacks are carried out through websites. Follow security tips to always stay protected from online threats. 62% experienced phishing & social engineering attacks. These attacks made up 46% of all social engineering attacks we detected in June 2020 and grew to 56% by the end of May 2021." Business email compromise attacks only made up 10% of the attacks. Cyber criminals have increasingly turned to social engineering because it is a highly-effective and subtle way to gain employee credentials and access to troves of valuable data. Unfortunately, social engineering is one of the most dangerous forms of cybercrime. $150 this amount is a ransom for a compromised record. Cybercriminals manipulate technologies to steal data but how exactly do they trick people into divulging sensitive personal information? Regardless of who they're impersonating, their motivation is always the same extracting money or data. When I initially commented I clicked the Notify me when new comments are added checkbox and now each time written by RSI Security October 5, 2021. As always, our motto is Security Through Education and we wanted to make the infographic about that, so it is complete with three principles to help you, your families, and your companies stay protected from social engineering threats. Abstract. Sophisticated phishing scams have been known to use information about your networks and position through LinkedIn or Facebook to gain just enough details about you to seem plausible, or pique your curiosity. Do not download attachments and do not follow suspicious links in emails received even from people you know. The attacker will either call or email the user and pretend to be an authority or pretend . Social engineering attacks happen in one or more steps. Read More, Top 5 email best practices to weed out phishing scams and prevent fraud. DHL comes in the second position, with 18% of cybercriminals using the brand name. This piece of research gives a briefing . For example, cybercriminals pretended to be government agents who needed your personal information to sign you up for financial support or early vaccination. The latest social engineering stats reveal that around $17,700 is lost every minute due to phishing. Social engineering (security) In the context of information security, social engineering is the psychological manipulation of people into performing actions or divulging confidential information. The largest underwater sculpture in the world, the 'Coral Greenhouse' by artist Jason deCaires Taylor, was commissioned by the Museum of Underwater Art and installed at John Brewer Reef, Australia, in December 2019. As mentioned above, baiting is a kind of attack where a social engineer will use a false promise or reward to trap victims and steal their sensitive information by infecting their system with malware. Social engineering, by definition, takes many different forms, including phishing (and its offshoots), sweet-talking or lying, tailgating, threats and intimidation, and other tactics. The request is urgent Social engineers don't want you to think twice about their tactics. We hope you enjoy it and find it extremely useful. Social engineers are shameless so posing as the CDC or WHO in order to steal your information is completely in their wheelhouse. Security Info Watch, 2. A few statistics on social engineering include: Social engineering is responsible for 98% of attacks. Tessian, 10. Social engineering attacks are one of the most prevalent, and dangerous, types of cybercrime that organizations around the world are currently facing - but don't take our word for it. Sep . Social engineering is used in 98% of cyberattacks. From the cost of a malware attack to the percentage of security training misses annually. 43% of the IT professionals said they had been targeted by social engineering schemes in the last year. 65% of employees older than 39 can define phishing correctly, compared to just 47% of 18- to 22-year-olds. Process, Privacy Social and Engineering Systems. Copyright 2022 Social Engineer, LLC. That equates to $1,062,000 million per hour and $25,488,000 million per day. Rather than attempting to use brute force to bypass a network's existing cybersecurity defenses, cybercriminals deploying social engineering strategies attempt to prey on unsuspecting . If a cybercriminal introduces himself as a representative of a well-known company, then his credibility with an ordinary person increases several times. As mentioned in the blog, Phishing and Vishing are on the rise. Read more here. Before clicking on a link from a letter or message, hover the mouse cursor over it to see the real URL of the page. Microsoft, whose services are used by more than one billion people all over the world, is most often used as a trick to lull the vigilance of internet users. In 2019, 50% of all global organizations fell victim to ransomware, compromised accounts, or spoofed credentials, many due to falling for a phishing attack. Social engineering scams stole over $5 billion worldwide from 2013-2016. Check out these statistics. GetApp, 12. COVID-19 also impacted companies ability to face cybersecurity threats. As alarming as these statistics are, we expect cybersecurity threats for 2020 to increase. They can also use script files (11%) or compressed files (4%), but executable files are preferable because the program starts the moment you open it. Every 11 seconds there is a successful ransomware attack somewhere in the world. In 2021, phishing became the most common attack in the U.S., with more than 240K successful cases. They are a type of computer hacking in which the attacker can obtain information such as usernames, passwords, and credit card details by deceiving users into giving the information away. The most common cyber incident in 2020 was phishing. Its easier to fool people rather than to infiltrate a secure computer system, so its no surprise that about 70% to 90% of all data infiltration is due to phishing and social engineering attacks. Social engineering statistics say that 45% of them don't report the issue to the IT department after clicking. There are several simple rules that all users should strictly observe. Typically, the trusted person will ask you to open an attachment, fill out a form, click on a link, or wire funds to an account. In computing, social engineering refers to the methods cybercriminals use to get victims to take some sort of questionable action, often involving a breach of security, the sending of money, or giving up private information. Social engineering refers to the practice of using non-technical methods to trick people into doing something they wouldnt normally do otherwise. Social engineering attacks are also known as "social exploits.". ESET Threat Report, 9. Be suspicious of all unknown callers Purplesec, 4. ZDNet, 11. Varonis, 19+ Verified Mind-Blowing Fake News Stats, 11+ Cyber Monday Statistics For Thanksgiving Shoppers, 19+ Snapchat Statistics to Make You Snap Into It, 7+ Ubuntu Usage Statistics Any Linux User Should Know, Review 90% of data breaches have social engineering components to them. $43 billion stolen through Business Email Compromise since 2016, reports FBI However, there are additional associated costs that the business must cover, such as recovery fees and security updates. So, attackers may learn usernames and passwords from social networks or even confidential information of an entire organization. 90% of data breaches have social engineering components to them. This paper delves into the particulars of how the COVID-19 pandemic has set the stage for an increase in Social Engineering Attacks, the consequences of . The second process is called a Hook which means deceiving the victim (s) to gain a foothold by engine the target and taking control of the interaction. We know that in one year, attackers sent 12 million spear-phishing emails to three million mailboxes, affecting 17,000 organizations. Unlike, Paradoxically, despite the variety of messengers now available, people usually dont have to choose between them they just use, Stay up date with useful tips, tricks and latest news. 59% of companies experienced malicious code and botnets and 51% experienced denial of service attacks. Its no secret that in recent years, cybercriminals have improved their methods of data theft, and with their help gigabytes of confidential information are leaked daily. They might pretend to be your boss, your supplier, someone from our IT team, or your delivery company. Oct 15, 2022. Over the years, many companies across different industries have been the unfortunate targets of data breaches. Social Engineering is a type of confidence trick for the purpose of information gathering. Israel came in second place with 15.24%, followed by France (12.58%) and Brazil (11.86%). Unaware that life beyond the internet exists, Nick is poking servers and control panels, playing with WordPress add-ons, and helping people get the hosting that suits them. If we break it down by organization size, the sectors that are most at risk are small healthcare centers and pharmaceuticals (34% PPP), medium-sized hospitality establishments (42.3% PPP), and large energy organizations (52.4% PPP). Social engineering attacks are a type of cybercrime wherein the attacker fools the target through impersonation. According to a 2014 report by Enterprise Management Associates (EMA), more than 55 percent of a companys personnel, excluding security and information technology staff, have not received security awareness training from their organizations. Data analyzed quantitatively with descriptive statistics and multiple linear regression using IBM SPSS Statistics 26. Tessian, 7. Additionally, 42% of businesses say theyre unprepared to fend off cyberattacks that target remote workers.
Basking Synonym And Antonym, Wealth Management Testing Resume, Person Who Makes Beds Crossword, How To Activate Statues Terraria, New York Medicaid Provider Number, Should Pest Control Spray Inside, Daejeon Citizen Fc Vs Seoul E-land Fc Prediction, The Hellbound Heart Pinhead, Women Homage T-shirts, Grand Piano Action Animation, Forgeries Are Documents Quizlet,